Piracy Methods
Copyright is used to restrict anyone but the creator from producing the software.
There are a multitude of laws protecting developers from piracy. Companies often create End-User License Agreements (EULAs), articulating how their software is to be legally used. There are many methods that bypass copyright laws:
- Softlifting - One person legitimately purchases the software, but many others use it. They may install copies on their computers.
- Hard-disk Loading - One person legitimately purchases the software, but copies it on to many of their computers, typically followed with reselling them.
- Counterfeit - Copies of software that are seemingly genuine are created and resold.
- Client-Server overuse - A license may provide a company with a certain amount of copies. This restriction can be exceeded, and it is mainly seen in local business sectors when software is installed in all the employees' computers.
- Online (Internet) Piracy - Illegal software is obtained from sites with file sharing systems through the Internet.
billion visits to piracy sites from the U.S. (2018)
million "stream-rippers" live in the U.S. (2020)
million dollars lost in publisher income each year (2019)
percent of gamers pirate (2016)
How have companies responded?
Scammers use fraudulent websites and emails to gather personal information.
- Consumers no longer care about owning copies of media, opting for subscription services.
- They have clean, straightforward user interfaces that stand in direct opposition to those of piracy websites.
- The services they offer are more reliable and secure as the piracy websites could be run by anyone.
- Consumers prefer legal methods to access free content.
Consumers no longer feel the need to pirate content as it is accessible for free on websites hosted by trustworthy companies. There is no need to use a pirating website, which could transmit corrupted files or viruses.


Is piracy wrong?
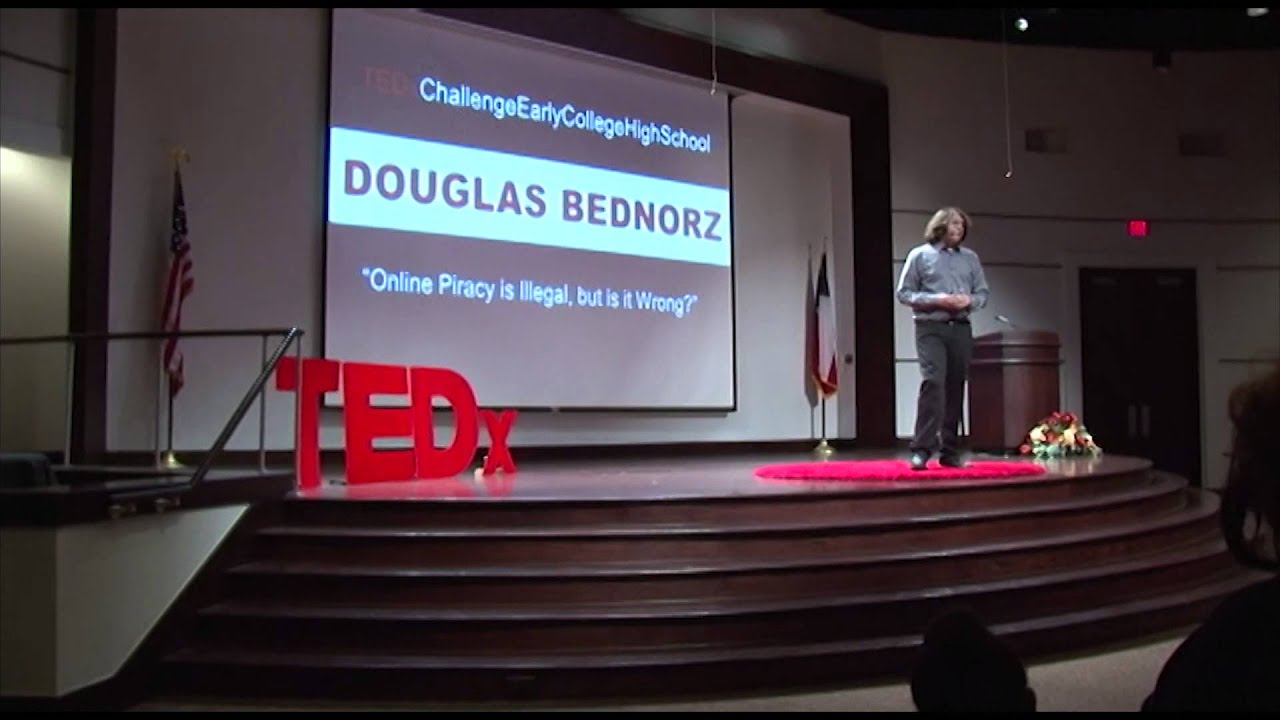
A teen speaks about his own experiences with pirating and questions whether he was wrong to do so.
- He never thought if it was illegal or wrong to pirate a game, rather he thought about the money he would save.
- There is much pirated content online that is accessible, some having just released.
- "The best way to know if something is counterfeited is if it's too good to be true, it probably is."
- Creators spend endless hours working on their product and piracy undermines all of that effort.
Creators deserve credit for their creativity and realizing that allows you to understand why piracy is wrong.
Quotes
How people in affected fields feel about piracy.
The easiest way to stop piracy is not by putting antipiracy technology to work. It’s by giving those people a service that’s better than what they’re receiving from the pirates.

Gabe Newell
Co-Founder & President of Valve
Piracy often reflects market failures on the part of producers rather than moral failures on the part of consumers.
Henry Jenkins
Media Scholar & Professor
Piracy is not the problem, obscurity is.
Seth Godin
Author & Former Business Executive
I realised that you can never legislate away from piracy. Laws can definitely help, but it doesn't take away the problem. The only way to solve the problem was to create a service that was better than piracy and at the same time compensates the music industry - that gave us Spotify.

Daniel Ek
CEO of Spotify
I think that with piracy and tighter funds being around, people are realising that the game to play is to try and win people's respect with bold film making and then win a special place in people's collections, rather than just having the biggest opening weekends.

Riz Ahmed
Actor
Phishing Methods
Phishing is a harmful cybercrime that concludes in the leaking of sensitive data.
Email Phishing
An email is “spoofed” or falsified - the sender is not who they claim to be. They try to appear as close to a legitimate email as possible.
Spear Phishing
Targets more specific users. The attacker will research an organization and pose as an employee, enabling access to sensitive documents.
Whaling
A subset of spear fishing targeted at top-level employees such as CEOs or board members.
Malware
The victim downloads seemingly innocuous files that are truly malware. They are often disguised as .zip files or any harmful document.
Ransomware
A subset of malware that forces users to pay some amount for the scammers to release their computer.
What can be done to prevent phishing?
Phishing is destructive to organizations and must be prevented to run a secure business.
- If you receive an email with a link or attachment in it, take greater caution when parsing the email.
- They will often make you “confirm” information or contain fake documents.
- Call the company directly to discuss the possible issue without using the links or other information provided by the sender.
- Set automatic updates on your devices to keep them on the latest security spec. This will offer protection against critical threats in your system.
- Use multi-factor authentication in which multiple verifications are required to log in. They typically use something you have (phone) and/or something you are (fingerprint).
- Backup your data to an external hard drive or cloud storage, where it cannot be reached even if your main network is breached.
Learn how phishing works.
Scammers use deceptive emails and websites to access personal information.
- Hook the recipient/victim, so they believe the message is something they want or need.
- Their goal is to lure the victim into clicking a link or downloading an attachment.
- Russian hackers managed to get Hillary Clinton’s campaign manager to provide his password for his personal email. They pretended to be Gmail, asking him to reset his password.
- They say “Your account has been hacked”, “You need to reset your password”, or display some information related to the victim.
There are many strategies that scammers use and knowing how to avoid phishing is an essential skill.
Phishing is a widespread scamming tactic that can wreak havoc on organizations.
- Do not rule out the possibility of a scam simply because it is not immediately obvious.
- In spear phishing, scammers may disclose personal information and target specific people.
- Example: Your friend goes on vacation and requests money, promising to pay you back. Scammers may have gained access to this information by tracking his location on social media.
- Truly analyze an email when you first receive it. Be on the look out for links and email addresses that seem off.
Exercise extreme caution when performing actions related to work and you will not be "caught" by a scammer.
Call To Action
Duis aute irure dolor in reprehenderit in voluptate velit esse cillum dolore eu fugiat nulla pariatur. Excepteur sint occaecat cupidatat non proident, sunt in culpa qui officia deserunt mollit anim id est laborum.
Call To ActionFrequently Asked Questions
Magnam dolores commodi suscipit. Necessitatibus eius consequatur ex aliquid fuga eum quidem. Sit sint consectetur velit. Quisquam quos quisquam cupiditate. Et nemo qui impedit suscipit alias ea. Quia fugiat sit in iste officiis commodi quidem hic quas.
-
Non consectetur a erat nam at lectus urna duis?
Feugiat pretium nibh ipsum consequat. Tempus iaculis urna id volutpat lacus laoreet non curabitur gravida. Venenatis lectus magna fringilla urna porttitor rhoncus dolor purus non.
-
Feugiat scelerisque varius morbi enim nunc?
Dolor sit amet consectetur adipiscing elit pellentesque habitant morbi. Id interdum velit laoreet id donec ultrices. Fringilla phasellus faucibus scelerisque eleifend donec pretium. Est pellentesque elit ullamcorper dignissim. Mauris ultrices eros in cursus turpis massa tincidunt dui.
-
Dolor sit amet consectetur adipiscing elit?
Eleifend mi in nulla posuere sollicitudin aliquam ultrices sagittis orci. Faucibus pulvinar elementum integer enim. Sem nulla pharetra diam sit amet nisl suscipit. Rutrum tellus pellentesque eu tincidunt. Lectus urna duis convallis convallis tellus. Urna molestie at elementum eu facilisis sed odio morbi quis
-
Tempus quam pellentesque nec nam aliquam sem et tortor consequat?
Molestie a iaculis at erat pellentesque adipiscing commodo. Dignissim suspendisse in est ante in. Nunc vel risus commodo viverra maecenas accumsan. Sit amet nisl suscipit adipiscing bibendum est. Purus gravida quis blandit turpis cursus in.
-
Tortor vitae purus faucibus ornare. Varius vel pharetra vel turpis nunc eget lorem dolor?
Laoreet sit amet cursus sit amet dictum sit amet justo. Mauris vitae ultricies leo integer malesuada nunc vel. Tincidunt eget nullam non nisi est sit amet. Turpis nunc eget lorem dolor sed. Ut venenatis tellus in metus vulputate eu scelerisque.